
Today’s networking equipment hums with activity, processing billions of packets every second. But how do network engineers glean insight from this vast sea of data? This post explains what network flow data is and how and why it is a critical network observability input.
________________________________________________________________________
What is Network Observability?
Network observability involves ensuring the reliability, security, and efficiency of modern networks. It encompasses data collection, analysis, visualization, alerting, troubleshooting, and understanding network issues in the context of historical data and trends. Moving beyond mere monitoring, it focuses on holistic approaches, broader visibility, and actionable insights.
_________________________________________________________________________
What is Network Flow Data?
Network flow data is typically collected from a variety of network devices such as routers, switches, and firewalls. These devices monitor and record the traffic passing through them, capturing details like source and destination IP addresses, port numbers, protocol types, and timestamps. This data allows for a comprehensive view of the network's activity and facilitates the analysis of communication patterns within the infrastructure.
Why Monitor Network Flows?
At its core, Network Flow Monitoring is about collecting, analyzing, and monitoring traffic across networks — be they vast or just segments. Such a tool isn’t just for pinpointing connectivity issues; it’s also crucial for identifying and mitigating potential security breaches.
By deploying flow monitoring, teams gain insights into:
Network load and performance
Which applications are in use
Where potential bottlenecks might form
Recognizing security anomalies
I. Understanding Network Flow Data:
A. Definition and Basics:
Network flow data, essentially records of device communications, includes information like IP addresses, ports, protocols, and timestamps. This data, typically collected by network devices, is fundamental in understanding digital interactions within an organization.
B. The Major Types of Network Flow Data:
NetFlow: A protocol from Cisco for collecting and monitoring network data, providing insights into traffic patterns and security threats.
sFlow: A sampling technology for scalable network monitoring, which samples packets to analyze network data.
IPFIX: The IP Flow Information Export, an IETF standard that extends NetFlow's capabilities, offering enhanced flexibility and vendor-neutral interoperability.
Public Cloud: AWS offers VPC Flow Logs, GCP provides VPC Flow Logs, and Azure has Azure Network Watcher's NSG Flow Logs. These services record information about the IP traffic flowing to and from network interfaces in VPCs or Network Security Groups (NSGs).
II. The Role of Network Flow Data in Cybersecurity:
Many don’t typically associate Network Observability with Network Security. At ElastiFlow, we see Network Observability more holistically, encompassing aspects of network security. Flow data monitoring is critical for any organization seeking to enhance their security posture against the increasing threat of internal and external attacks. Read this post for a more detailed discussion - "Security Incident! Revealing Every Nefarious Network Event and Rising to the Challenge of Compliance".
A. Threat Detection and Prevention:
Anomaly Detection: Identifying unusual data traffic patterns to detect potential security breaches.
Intrusion Detection Systems (IDS): Analyzing flow data to identify and respond to suspicious activities.
B. Incident Response and Forensics:
Traceability and Accountability: Using flow data for post-incident analysis to trace the origin and impact of breaches.
Forensic Analysis: Leveraging flow data as a digital fingerprint for reconstructing security incidents.
C. Regulatory Compliance:
Network activity and verification: Flow data is crucial for regulatory compliance as it provides detailed records of network activity, enabling organizations to monitor and verify the handling of sensitive information. This granular visibility ensures adherence to data protection laws and regulations, as it allows for the tracing and auditing of data flows.
III. Optimizing Network Performance:
A. Bandwidth Utilization:
Traffic Analysis: Insights into bandwidth usage for optimizing network performance.
QoS (Quality of Service): Prioritizing critical applications using flow data to manage traffic effectively.
B. Capacity Planning:
Identifying Bottlenecks: Using historical data to anticipate and plan for future network needs.
IV. Compliance and Regulatory Requirements:
A. Data Governance:
Monitoring Data Flows: Ensuring compliance with data protection laws by monitoring sensitive information flows.
Auditing and Reporting: Facilitating adherence to regulatory requirements through detailed flow data records.
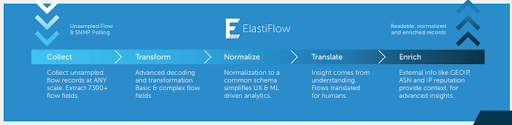
V. ElastiFlow - Making Flow Data Observable
One of the most challenging aspects of network observability is getting the Flow data you need into the data platform of your choice in a common schema. ElastiFlow's NetObserv has done the heavy lifting. NetObserv enables you to collect flow data from routers, switches, firewalls and hosts, and standardizes the records into a common schema. All major vendors are included - Cisco, Arista, Riverbed, Juniper, Palo Alto Networks. ElastiFlow then enriches the data with Geo, ASN, Threat-Intel, DNS, BGP and user-defined business context, and sends the metadata to your favorite open data platform so that you can start generating the visualizations you need for your own use cases or the ones that we have preconfigured.
Conclusion:
Network flow data is more than just traffic monitoring; it's a key element in cybersecurity, network performance optimization, and regulatory compliance. Understanding the different types and its potential empowers organizations to protect their digital assets and maintain an efficient network infrastructure. ElastiFlow offers a comprehensive solution for network observability, with a free trial and flexible pricing options. Start your trial today!
Update June 2024: Since publishing this post, ElastiFlow has launched NetIntel, a product that enhances and enriches flow data with significantly more threat intelligence information.
Stay connected
Sign up to stay connected and receive the latest content and updates from us!